What is FirewallD?
Firewalld was introduced in CentOS 7/ RHEL 7 with both a GUI and command line interface for making changes. It is a alternative for using IPtables. If offers a zone based firewall configuration that allows you to enable different zones with different levels of trust.
Different Zone possibilities
Zones change be changed, different network cards or rules can also force different zones to be applied in different situations.
Drop Zone – Allows outgoing connections, but incoming connnections are dropped
Block Zone – Allows outgoing ssh/dhcp connections, but incoming connnections are rejected.
Public Zone – Allows both incoming and outgoing connections(ssh)
DMZ Zone – Allows both incoming ssh connections and outgoing connections
Trusted Zone – allows both incoming and outgoing connections
Home – dhcp,ipp and ssh incoming is allowed as well as outgoing connections
Internal – Outgoing connections and the same connections as Home are allowed
FirewallD Zone Management
To see what zone is currently being used:
# firewall-cmd --get-default-zone internal
To set a new zone(replace internal with the zone you want to use)
# firewall-cmd --set-default-zone=internal success
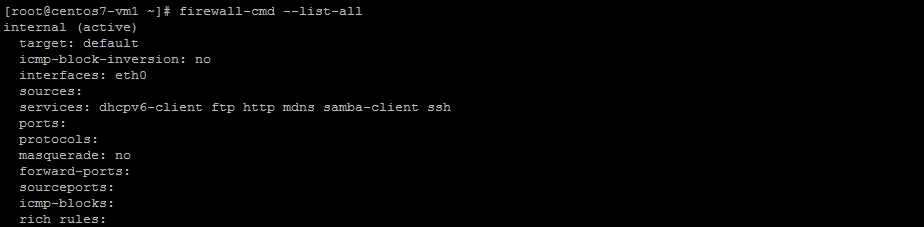
To see configuration of a zone:
# firewall-cmd --list-all public (active) target: default icmp-block-inversion: no interfaces: eth0 sources: services: dhcpv6-client ftp http https ssh ports: 80/tcp 81/tcp protocols: masquerade: no forward-ports: sourceports: icmp-blocks: rich rules:
FirewallD Port Managment
To allow ftp to access with the current zone being used:
# firewall-cmd --add-service ftp success
To allow http access with the current zone being used:
# firewall-cmd --add-service http success
If you add –permanent this will ensure the rule stays after a reload of the firewall ruleset.
To get a list of all services:
# firewall-cmd --get-services RH-Satellite-6 amanda-client amanda-k5-client bacula bacula-client ceph ceph-mon dhcp dhcpv6 dhcpv6-client dns docker-registry dropbox-lansync freeipa-ldap freeipa-ldaps freeipa-replication ftp high-availability http https imap imaps ipp ipp-client ipsec iscsi-target kadmin kerberos kpasswd ldap ldaps libvirt libvirt-tls mdns mosh mountd ms-wbt mysql nfs ntp openvpn pmcd pmproxy pmwebapi pmwebapis pop3 pop3s postgresql privoxy proxy-dhcp ptp pulseaudio puppetmaster radius rpc-bind rsyncd samba samba-client sane smtp smtps snmp snmptrap squid ssh synergy syslog syslog-tls telnet tftp tftp-client tinc tor-socks transmission-client vdsm vnc-server wbem-https xmpp-bosh xmpp-client xmpp-local xmpp-server
Managing the service itself
To start firewalld
systemctl start firewalld
To ensure firewalld starts after a reboot
systemctl enable firewalld
To reload the firewalld rulset:
firewall-cmd --reload